So, you’re diving into FIPS compliance, huh?
Honestly, it sounds way more boring than it really is. But stick with me here.
You might be thinking, “What even is FIPS?” It’s basically this standard that keeps our data safe and secure. Super important stuff!
But here’s the kicker: lots of organizations struggle with it. They either don’t know where to start or just feel overwhelmed.
Let’s break it down together! I’ll share some best practices that can actually make this a lot easier for you.
Understanding FIPS Compliance Requirements: A Comprehensive Guide for Legal Professionals
FIPS Compliance Requirements Explained: Essential Insights for Technology Implementation
Understanding FIPS compliance can feel like wading through a thick fog, especially for legal professionals who might not be as tech-savvy. But trust me, it’s really important to get your head around it, especially if you’re dealing with sensitive government data or working with organizations that are subject to these regulations. FIPS stands for the Federal Information Processing Standards, which are basically security standards set by NIST (National Institute of Standards and Technology). So let’s break this down in a way that makes sense.
What Does FIPS Compliance Mean?
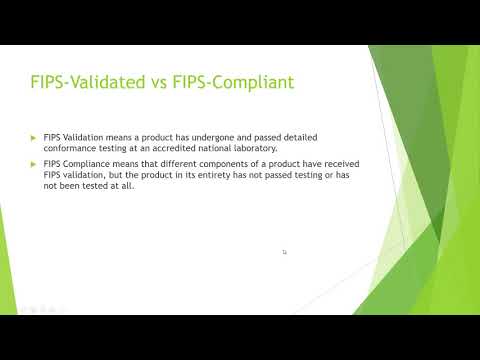
Essentially, when something is FIPS compliant, it means it meets certain security requirements laid out by the federal government. This is critical if you’re developing software or handling sensitive information. For example, if your law firm is using cloud services to store client data, you’ll want to ensure those services comply with FIPS. If they don’t, the data could be at risk.
Why Is It Important?
Well, think of it this way: complying with FIPS can protect not just your organization but also your clients. When you’re dealing with sensitive client information—like social security numbers or confidential legal documents—the last thing you want is a data breach. A solid understanding of compliance requirements can help safeguard against that.
Key Components of FIPS Compliance:
- Cryptographic Modules: These are essential for protecting sensitive information. They must meet specific security levels under the Federal Information Processing Standard 140-2 (FIPS 140-2). This means any encryption software used should be validated against these standards.
- Documentation and Testing: Organizations must provide thorough documentation showing how their systems meet the compliance requirements. This often includes detailed testing procedures that confirm effectiveness.
- Regular Audits: Compliance isn’t a one-time deal; you have to keep checking back to ensure everything remains secure according to evolving standards.
A Practical Example:
Imagine your firm decides to use a new case management software that doesn’t comply with FIPS but promises great features. If this software isn’t secure enough and gets hacked, you could end up exposed—both legally and financially. Not fun!
Navigating Implementation:
If you’re involved in implementing or overseeing any tech solutions at your organization, start by doing a comprehensive audit of your current tools. Ask questions like:
– Is our current encryption meeting FIPS 140-2?
– Are we routinely testing our systems for vulnerabilities?
Additionally, bringing in a cybersecurity expert can make things easier! They can bridge the gap between law and tech more smoothly than most folks.
Conclusion:
In short, grasping FIPS compliance requirements isn’t just about ticking boxes—it’s about ensuring there’s a solid foundation for handling sensitive data securely. For legal professionals like yourself navigating this landscape, being informed makes all the difference!
Comprehensive Guide to FIPS Compliance: Essential List of Requirements and Standards
FIPS Compliance List: Key Technologies and Standards for Secure Systems
FIPS, or the **Federal Information Processing Standards**, are a set of guidelines for managing information and ensuring security in the U.S. government. It’s a big deal for organizations that handle federal data, and being compliant can feel like navigating a maze at times. Let’s break it down.
FIPS compliance essentially means your systems meet certain security standards that help protect sensitive info. If you’re working with federal data, understanding these requirements is crucial. So, what should you know?
Key Requirements:
Many of those standards revolve around encryption and information security practices to keep data safe from unauthorized access. Here are some major points to consider.
- FIPS 140-2: This standard focuses on cryptographic modules—basically, it checks if your encryption methods are secure enough. You must use algorithms approved by NIST (National Institute of Standards and Technology).
- FIPS 199: This one’s about categorizing information based on its impact level—low, moderate, or high—on organizational operations or assets.
- FIPS 200: It outlines minimum security requirements for federal information systems by focusing on implementing basic safeguards.
You see? It’s all about defining how you protect sensitive data.
Key Technologies:
To be FIPS compliant, you need the right tech tools in place. A few essential technologies include:
- Encryption Software: Solutions like AES (Advanced Encryption Standard) help secure data in transit and at rest.
- Access Controls: These should be strict! Make sure only authorized individuals can access sensitive areas of your system.
- Monitoring Tools: Using tools that track activities can help spot any unusual behavior that might suggest a breach.
And hey, while these technologies are essential, it’s not just about slapping them on your systems and calling it a day.
Best Practices:
It’s important to develop an entire culture around compliance in your organization:
- Regular Training: Make sure everyone knows the importance of FIPS compliance and understands how to do their part.
- Continuous Monitoring: Regularly check if your systems remain compliant with FIPS guidelines as they evolve over time.
- Audits: Conduct routine audits to ensure all processes are being followed correctly; catch issues before they become problems!
Oh man, I once worked with an organization that neglected regular audits and ended up facing some serious penalties when their non-compliance was discovered during a random check!
Being proactive makes all the difference here.
The Takeaway:
So basically, FIPS compliance isn’t just some checkbox you tick off. It’s about instilling robust security practices throughout your organization while leveraging the correct technologies. Follow these core requirements and best practices; you’ll be well on your way to keeping sensitive information safe! Just remember: staying informed is essential since standards do change over time!
Understanding FIPS 140-2: Key Compliance Standards for Data Security in Government and Industry
FIPS 140-2 Explained: Essential Insights into Cryptographic Security Standards for Technology Solutions
FIPS 140-2, or the Federal Information Processing Standard, is all about data security. Basically, it lays out the requirements for cryptographic modules used by government agencies and contractors. If you work in tech or manage sensitive data, understanding this standard is key.
So, what’s the deal with FIPS 140-2? Well, it has four levels of security. Each level builds on the previous one to meet specific needs for protecting sensitive information. Here’s a quick breakdown:
- Level 1: This is the most basic level. It requires just some security requirements without specific cryptographic mechanisms.
- Level 2: This one adds physical security measures to prevent tampering.
- Level 3: At this level, you get strong physical security plus requirements for identity-based authentication.
- Level 4: The highest level! It includes everything from previous levels plus more stringent physical and environmental protections.
Let me tell you a little story to make this clear. Imagine a friend of yours has a diary filled with secrets (alright, maybe it’s just their thoughts on pizza toppings!). They might keep it in their room (Level 1), then they might lock it (Level 2), later they could even use a fingerprint scanner (that’s Level 3), and at last, they move it to a safe under several layers of protection against real-world threats (you guessed it—Level 4).
Now, implementing FIPS compliance isn’t just about getting certified. It’s about best practices too. You need to ensure that your systems are well-documented and regularly tested. Organizations should focus on:
- Risk Assessment: Regularly assess risks and vulnerabilities that could affect your critical data.
- Documentation: Keep everything documented from procedures to mechanisms in use for transparency.
- Training: Make sure your team understands these standards and knows how to maintain compliance.
- Testing: Conduct ongoing tests of your cryptographic modules against FIPS requirements.
You see? Keeping everything in check makes it easier in case there’s an audit or if something goes wrong.
FIPS compliance brings some serious perks too! Besides staying on the right side of regulations, it can enhance your organization’s reputation by showing clients that you take data security seriously. Plus, using certified cryptographic modules can help prevent costly breaches which can tarnish trust.
In short, understanding **FIPS 140-2** isn’t just for tech whizzes; if you’re involved with data security at any level, it’s essential knowledge. Keep those best practices front and center while making sure your team stays sharp about standards—it’s like keeping that diary safe!
FIPS compliance, which stands for Federal Information Processing Standards, can feel a bit like diving into the deep end of the pool for some organizations. It’s one of those things where you know you should care, but figuring out what it really means and how to stick to it can be a bit overwhelming. I remember the first time my buddy had to deal with compliance standards at his job. He was stressed out about ensuring everything was up to snuff, and it wasn’t until he broke it down that he realized it wasn’t as scary as it seemed.
So, basically, FIPS is all about security in handling sensitive information—especially for federal agencies and those working with them. If your organization is involved in that world, you probably already know that staying compliant isn’t just a good idea; it’s necessary. But here’s the kicker: adhering to these standards can also build trust with your customers and partners.
One best practice that always comes up is understanding what specific FIPS standards apply to you. There’s really no one-size-fits-all approach since different organizations have different needs. It’s essential to take an inventory of your systems and data. You wouldn’t want to accidentally overlook some sensitive data stashed away on an old server somewhere! Trust me; I’ve seen organizations get caught off guard because they didn’t account for every little thing.
Then there’s training the team. Seriously, if everyone knows the score about FIPS—from IT staff to management—you’ll find it way easier to keep everything on track. It’s like trying to win a game without knowing the rules—it just doesn’t work!
Implementing strong encryption practices is another solid move. Encryption isn’t just tech jargon; it’s like wrapping your secrets in a cozy blanket so only those who are supposed to see them can peek inside. This becomes especially relevant when dealing with data at rest or in transit.
You’ll want regular audits too! Think of them as check-ups for your organization—making sure there are no nasty surprises hiding under the surface is key. And while this might sound like more work on top of everything else you’re juggling, consider how much smoother things will run when you’re proactive rather than reactive.
Lastly, think about documenting everything. You might feel like you’re writing a novel sometimes—who wants to do paperwork? But documentation can save you when audits come calling or when things go haywire.
In all honesty, keeping FIPS compliance in check might seem daunting at first glance, but breaking it down into these simple practices makes navigating through a lot less painful—and who knows? It might even become second nature after a while!