So, picture this: you’re chilling at home, scrolling through your phone, and suddenly your computer starts acting all weird. You know what I mean? Pop-ups everywhere, maybe some strange emails popping up. That’s when you realize—oh no! Your network security might be in trouble.
Now, if you happen to have a Fortinet Firewall, that’s a solid first step. But just having it isn’t enough. You’ve gotta keep an eye on it! Monitoring is key here.
Let’s chat about some tools and techniques you can use to make sure everything’s running smoothly. Seriously, keeping your digital space safe doesn’t have to be a headache. It can actually be pretty straightforward!
Top 3 Network Monitoring Tools for Enhanced IT Management
When it comes to network monitoring, having the right tools can make all the difference in managing your IT environment effectively. You want something that’s easy to use yet powerful enough to give you insights into what’s happening on your network. Here’s a rundown of three popular network monitoring tools that can help you keep an eye on things, especially if you’re working with a Fortinet firewall.
1. PRTG Network Monitor
PRTG is like that overachiever in class who just gets everything done. It monitors your entire network, from bandwidth usage to the health of your devices. Basically, it has sensors that check every aspect of your network traffic and performance. So if there’s something off—let’s say your Fortinet firewall isn’t performing as it should—PRTG can alert you right away. It also has a user-friendly interface that displays information through customizable dashboards. Seriously, you get to see graphs and maps that make understanding data way easier!
2. SolarWinds Network Performance Monitor
If PRTG is the overachiever, SolarWinds is like the athlete who also gets good grades—it’s powerful but requires some setup time initially. This tool excels in providing deep insights into network performance, which is essential when managing something as important as a Fortinet firewall. It features robust reporting tools and alerts for any unusual activity or performance issues. Plus, its interface doesn’t compromise on usability either; it balances ease with powerful features well.
3. Nagios
Now let’s chat about Nagios—this one’s more for folks who are comfortable diving deep into configurations and setups because it’s a bit more technical than the previous two options. Nagios allows you to monitor various components like servers, applications, and services in real-time but expect a learning curve here! It gives you great flexibility in terms of plugins and customizations so you can tailor it for specific needs related to your Fortinet firewall management.
So when you’re looking at enhancing IT management through network monitoring tools, consider how these options fit into what you’re trying to achieve. Each tool offers unique features, and finding the one that aligns with your specific needs will save you headaches down the road!
Understanding FortiClient Tools: Features, Benefits, and Use Cases
FortiClient is a security suite that works hand in hand with Fortinet’s firewalls. It’s designed to protect various devices, whether they’re laptops or mobile phones, from threats like viruses and malware. So, if you’re wondering what it actually does and how it can help you, let’s break it down.
Key Features of FortiClient
First off, let’s talk about the main tools within FortiClient:
- Antivirus Protection: This feature scans your files and programs for harmful software. It tries to catch issues before they become a problem.
- VPN Support: With a Virtual Private Network (VPN), your internet connection stays secure while you’re online. It’s super helpful for remote workers who need to connect to company networks safely.
- Web Filtering: This tool blocks access to malicious websites that might try to steal your data. It’s kind of like having a bouncer for your browser!
- Application Firewall: This monitors application activity. It can block suspicious behavior from apps that might seem innocent but could be risky.
- Endpoint Management: Admins can manage devices remotely, ensuring they’re protected and compliant with corporate policies.
Each of these features plays a role in keeping your computing experience safe.
Benefits of Using FortiClient
Now that we know the features, what’s in it for you? Here are some benefits:
- Simplicity: The user interface is pretty straightforward. You don’t need to be a tech whiz to navigate through it.
- Comprehensive Protection: It covers multiple threat vectors – from web threats to device vulnerabilities – offering rounded security.
- Integration with Fortinet Firewalls: If you already have a Fortinet firewall set up, using FortiClient is a no-brainer since they work seamlessly together!
So basically, it’s about making your life easier while keeping your data safe.
Anecdote: A Close Call
I remember this one time when I was working on my laptop at a coffee shop. Suddenly, my screen went all weird – like something out of a horror movie! Turns out, I clicked on what I thought was an innocent ad. But luckily, I had something like FortiClient running; it blocked the malicious site before I could get into trouble! Just one experience like that makes you appreciate good security software.
Use Cases for FortiClient
Now let’s chat about when you’d actually want to use this thing:
- Tightly-Controlled Environments:If you’re running an office where sensitive client information is handled daily, this tool helps keep everything locked down tight.
- If employees are working from all over – think home or even while traveling – having VPN and endpoint protection becomes crucial.
- Poking around on public Wi-Fi? Having FortiClient ensures you’re extra cautious while browsing.
You see? There are plenty of situations where having this sort of security can save the day.
In summary, understanding what FortiClient brings to the table gives you peace of mind. With its robust features and practical benefits tailored toward everyday use cases, it’s easy to see why folks would choose it—especially if they already rely on Fortinet’s firewall solutions!
Understanding FortiGate: Two Key Methods for Traffic Inspection
When it comes to network security, FortiGate firewalls offer some powerful tools for traffic inspection. You know, when you’re trying to keep out unwanted visitors while letting friends in? That’s what FortiGate does for your network. So, let’s break down the two main methods of traffic inspection that FortiGate uses.
First up, we have the Flow-based Inspection. This method is all about speed and efficiency. It inspects the header information of packets—think of it like checking an ID at a club before letting someone in. If everything seems legit, the data flows right through without digging deeper into the content. This method is super useful for high-speed networks where speed is critical.
But here’s the catch—while flow-based inspection is fast, it doesn’t look at the actual content within the packets. So if there’s something suspicious hiding under that surface, it might get through unnoticed. For example, if a malicious file tries to sneak in disguised as a normal-looking email attachment, flow-based inspection might just wave it on through.
Then we’ve got Proxy-based Inspection. This one’s like having a bouncer who checks not just IDs but also gives each person a pat-down before they enter! The proxy acts as an intermediary between users and the internet. When data requests come in, they go straight to this proxy first.
Now, with proxy-based inspection, every packet is fully analyzed—not just its header but its entire content! Yep, this means catching those sneaky threats hiding behind seemingly safe data streams. It can slow things down a bit since there’s extra processing involved, but hey—it gives you peace of mind knowing you’re safer from potential threats.
So here’s the deal: both methods have their pros and cons and choosing between them depends on what your network needs most. If you’re looking for speed and can live with some risk? Flow-based might be your pick. But if security’s your top priority and you’re willing to trade off some speed? Go with Proxy-based inspection.
You know, firewalls are like the digital bouncers of our networks, right? They keep out the troublemakers and let the good stuff in. Fortinet’s firewalls are pretty well-known in that space. If you’ve ever had to deal with network security, you probably realize how vital monitoring is. It’s not just about setting up a firewall and hoping for the best—it’s like putting up a “No Entry” sign but leaving the door wide open.
When I was working on a project once, we installed a Fortinet firewall at this small office. Everything was going smoothly until one day, we noticed some strange spikes in traffic. Turns out, someone had been poking around our network trying to access sensitive info! That’s when I learned how crucial monitoring tools are.
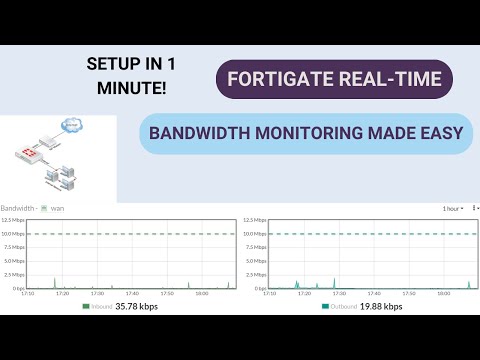
Fortinet offers some solid features for keeping an eye on things. With their management software, you can get real-time visibility into your network traffic. This means you can see who’s chatting with who, what devices are connected, and whether there are any unusual patterns emerging. You could say it’s like having a security camera for your data flow.
Then there’s logging! Oh boy, logs can be overwhelming if you don’t know what to look for. But those detailed records help you review what happened during an incident or even predict future issues based on past behavior. The trick is knowing how to sift through it all without losing your mind.
And then we have alerts! Seriously, it’s amazing but also kind of terrifying how quickly stuff can change online. Setting up alerts guarantees you’ll be informed if something suspicious goes down—like if someone tries to brute-force log into your system or if there’s unauthorized device trying to connect.
Honestly, keeping everything in check takes time and attention. But once you get into the rhythm of monitoring with these tools and techniques from Fortinet—it becomes second nature. You feel more secure knowing that you’re on top of things instead of waiting for disaster to strike.
At the end of the day, having strong firewall monitoring isn’t just about preventing attacks; it’s about understanding your network better so you can plan ahead and make informed decisions! It’s like having that trusty umbrella—you may not need it all the time but when a storm rolls in unexpectedly? Man, are you glad you have it!