You know, when it comes to keeping your data safe, sometimes the little things matter most. Ever heard of database roles? They’re like the bouncers at a club, making sure only the right people get in.
Think about it. With all the hackers and data leaks out there, having a solid security system is key. Roles make sure that individuals only see what they need to see.
And compliance? Oh man, that’s a whole other story. Keeping up with regulations can feel like running a marathon in flip-flops. But with proper roles in place, you can actually breathe easier.
So let’s chat about how these database roles can totally amp up your security game and help keep everything above board!
Enhancing Database Security: The Role of User Permissions and Access Control
Understanding how to enhance database security is super important, especially when it comes to user permissions and access control. Basically, the better you manage who gets in and what they can do, the safer your data becomes.
First off, user permissions are like the locks on your doors. They determine who can see or change your data. You wouldn’t want just anyone wandering into your house, right? The same logic applies here. You create different levels of access based on roles within the organization.
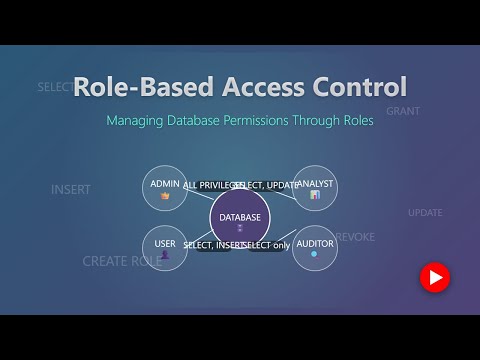
In most databases, there are several roles you can define:
- Admins: These folks have full access to everything. They can create and delete users, manage data, and adjust settings.
- Editors: Editors can modify existing records but might not have permission to delete anything.
- Viewers: These users can only look at the data without altering anything. Think of them as guests in a gallery—they can admire but not touch.
Now, access control fits right in here, working alongside those permissions to ensure that people are accessing only what they need for their job. It’s like a VIP section at a concert—only certain people get in! You set up rules that dictate how different roles interact with data.
For example, if an employee only needs read access to financial reports for their job in marketing, you give them that limited permission instead of letting them tamper with sensitive information. This limits risk considerably!
It’s also crucial to regularly review these permissions. Employees change roles or leave—sometimes keys just get lost! Regular audits help ensure that former employees don’t retain access they shouldn’t have anymore.
Another cool aspect is implementing a principle called least privilege. This means giving users only the minimum level of access necessary for their work. If someone needs to view customer information once a month for reporting reasons, why give them full access all year around? It reduces risk!
And speaking of risk reduction, encryption plays a part too! Even if someone somehow gets unauthorized access through some loophole (let’s hope not!), encrypting sensitive data means all they see is jumbled gibberish without the decryption key.
In sum, by carefully managing user permissions and using strict access control measures with regular reviews and adhering to principles like least privilege and encryption practices, you really strengthen database security. It just makes sense—protecting your valuable data means protecting your whole operation!
Exploring the Advantages of Using Roles in Database Security
When talking about database security, one of the key concepts that can really make a difference is the idea of roles. So, let’s break this down. Roles in a database are like job descriptions for users or groups. Instead of giving everyone full access to everything, you assign roles based on what they need to do.
This approach brings a bunch of advantages. First off, it enhances security. By limiting what each user can see and modify, you reduce the chances of someone unintentionally—or intentionally—messing things up. Imagine if you gave your kid the keys to your car without any restrictions. Not so smart, right?
- Granular Access Control: Roles allow for very specific access levels. For instance, a role might only let someone read data but not change it. That’s super important in environments where sensitive information is involved.
- Simplified Management: Managing roles is easier than tracking individual permissions for hundreds of users. If someone leaves or changes positions, you just update their role instead of reconfiguring every single permission.
- Compliance Made Easy: Many industries have strict regulations regarding data access. Using roles helps demonstrate compliance by providing clear documentation on who has access to what.
A practical example could be an online shopping site. You might have different roles like admin, customer support, and regular users. Each role has specific permissions like updating product listings, responding to customer inquiries, or simply browsing products. This keeps things organized and secure.
The beauty of using roles also lies in how they can be combined with other security measures like a two-factor authentication system. So even if someone had unauthorized access to a role, gaining full entry requires extra verification—which is just smart thinking!
If done properly, implementing roles enhances accountability as well since it’s easier to track actions taken by users based on their assigned roles. You know who did what when something goes wrong—that’s key!
So basically, using database roles isn’t just a technical choice; it’s a strategic move that protects your data while keeping management efficient and compliance-friendly. When set up right, they really are a game changer in maintaining robust database security.
Understanding Data Security Measures in Database Systems
When it comes to database systems, data security measures are a big deal. You definitely don’t want sensitive information floating around without any protection, right? And that’s where database roles come into play. They’re like little gatekeepers, managing who has access to what.
Database roles help you define permissions based on job functions. So instead of giving everyone the same level of access, you can tailor it to their needs. For instance, a data analyst might need read-only access to certain tables, while a developer may need more extensive privileges for testing purposes. You get where I’m going with this?
- Separation of Duties: One key aspect is the separation of duties. This means that no single person should have full control over everything. If someone can both create and delete records, that’s like giving a kid the keys to your car!
- Granular Permissions: With roles, you can set granular permissions. Imagine having different roles for finance, HR, and IT—all tailored with specific rights! It’s much safer than just winging it.
- Auditing: Roles also help in auditing activities. If something goes wrong or data gets mishandled, tracing back who did what becomes way easier when you’ve got clear roles defined.
- Compliance Needs: Many industries have strict compliance regulations (think GDPR or HIPAA). Having clear database roles doesn’t just enhance security; it helps you stay compliant too!
The reality is that without these measures in place, the risk of data breaches increases dramatically. Remember that big data leak a few years back? Yeah, not fun! But with well-defined database roles, you lower those risks significantly.
You know how sometimes it feels chaotic when everyone has access to everything? Well, implementing these measures creates a structured environment that keeps things in check and ensures everyone knows their boundaries.
If you think about it logically—why give someone all the tools when they only need one or two? Less access brings less risk!
The thing is, while implementing these security measures might seem like extra work at first glance, they pay off big time in the long run by protecting your valuable data and maintaining trust among users.
You see? Understanding and utilizing data security measures, especially through database roles can make a world of difference! You not only defend your databases against unauthorized access but also promote responsible use among team members.
So, you know, when it comes to managing data, security is like a huge deal. I remember this one time at my old job where we had a major scare with sensitive client information getting accessed without permission. It was a wake-up call! That’s when I really started paying attention to how important database roles can be for security and compliance.
Basically, database roles help organize and control who gets to see or do what with the data. Imagine it like a team in a company: not everyone needs access to sensitive information, right? You wouldn’t let the janitor into the executive board meetings just because they have a key. Same concept here! Roles can be assigned based on job responsibilities, making sure that only the necessary people have access to certain data.
This is super useful for compliance too. Companies have to follow certain regulations like GDPR or HIPAA, and if they don’t? Well, it could mean hefty fines or loss of trust from clients. By carefully defining database roles, businesses can demonstrate that they’re handling data responsibly and in line with these regulations.
And you know what’s cool? If something changes—like if an employee switches departments—you just modify their role instead of reworking everything from scratch. It makes managing access way simpler and keeps things organized.
Sure, setting these roles up takes some thought and planning upfront but trust me; in the long run, it’s totally worth it for peace of mind knowing that your data’s safer than ever!