So, you’re diving into Azure, huh? Cool! It’s like this massive cloud playground where you can do all sorts of awesome stuff. But then there’s that whole guest access thingy.
Setting up a guest account may sound a bit tricky at first. You might be thinking, “Do I really need this?” Well, yeah! It’s super handy for collaborating without giving away the keys to your castle.
Imagine inviting a friend over to use your gaming setup but wanting to keep them from messing up your files. That’s kind of the vibe here. You want secure access without losing control of your stuff.
Let’s break it down together and make it easy-peasy!
Step-by-Step Guide to Creating a Guest Account in Windows 11
Creating a guest account in Windows 11 is pretty straightforward, and it can really help when you want to let someone use your PC without giving them access to all your personal stuff. So, let’s break down how to do it step by step.
First off, you need to open the **Settings** app. You can get there by clicking on the **Start** button (the Windows logo) and then selecting the gear icon for Settings. Alternatively, you could just hit **Windows + I** on your keyboard, which is super quick!
Once you’re in Settings, look for the **Accounts** section. Click on it and then choose **Family & other users** from the left-hand menu. This is where you’ll manage user accounts on your PC.
Now here comes the fun part! In the Family & other users section, you’ll see an option that says **Add someone else to this PC**. Give that a click. A window will pop up asking you how you want to add a user. Here’s where it gets slightly tricky:
– You’ll see an option for entering an email or phone number for a Microsoft account, but instead, look for “I don’t have this person’s sign-in information” and click on it.
– After that, select “Add a user without a Microsoft account.” This is super important because you want to create a local guest account.
Next, you’ll be prompted to create a username and password (you can skip the password if you want). Just fill that part out; remember to keep it simple since this is just for guests.
Important: Make sure to note down this information if you’ve set a password—guests will need it!
Once you’ve set up that info and clicked next, your new guest account will be created! Now back in the Family & other users section, find your newly created account—you may need to refresh the view or scroll down a bit. Once you spot it, click on it and select **Change account type**.
Here’s where we make sure everything’s set right: change the account type from “Standard User” (which is what we usually use) to “Guest”. While Windows 11 doesn’t exactly label guest accounts anymore like older versions did, setting permissions correctly helps keep things separate.
Now with everything in place, when someone logs into that guest account:
– They won’t see any of your personal files.
– They won’t be able to mess with system settings like installing software or accessing sensitive data.
And there you go! Your guest can now use your computer without snooping around in your stuff—which makes life easier when friends or family pop by.
You might also consider creating some ground rules about what they can do while using your device—it keeps everything clear and avoids any bumps later!
Just remember: whenever they log out or shut down their session, all data they created during their time using that account won’t save—so it’s perfect for short visits! But if you’re looking at longer-term access needs or more complex setups like Azure Guest Accounts for secure environments? That might require different steps altogether since those involve more advanced configurations related to cloud management.
And that’s about it! It’s helpful having those extra layers of control over who messes with what on your computer—you follow me? If something goes wrong while setting this up—don’t worry; just double-check each step we talked about!
Understanding Guest Accounts in Entra ID: Key Features and Best Practices
Maximizing Security and Collaboration with Guest Accounts in Entra ID
Understanding Guest Accounts in Entra ID can seem a bit daunting at first, but once you break it down, it’s pretty straightforward. Basically, guest accounts let you share resources with people outside your organization while keeping things secure. Think of it as giving someone a visitor’s pass. They can access certain areas without the keys to everything.
Key Features of Guest Accounts
One of the standout features is **collaboration**. With guest accounts, users from different organizations can work together on projects using tools like Microsoft Teams or SharePoint. You can invite a consultant or a client to join a team without creating a whole new user account in your system. It’s like sending an invitation to your birthday party—only they get to play on your games without moving in with you.
Another important aspect is **security controls**. You can set permissions for guest users really easily—limit what they see and do based on their roles. So, if they only need access to one document or project, you’re not accidentally letting them into everything else.
Also, with Entra ID, you have the ability to monitor these guests’ activities through auditing logs and reports. This means if something funky happens, you’ve got eyes on what’s going down.
Best Practices for Utilizing Guest Accounts
So how do you make the most outta these guest accounts? Here’s where best practices come into play:
- Limit Permissions: Only give them access to what’s necessary for their tasks. If they only need one document, don’t grant them full library access.
- Set Expiration Dates: If the collaboration is temporary, set an expiry date on their access. This helps keep things tidy and secure.
- Regularly Review Access: Make it a habit to check who has access every few months. It’s like cleaning out your closet; sometimes you just need to let go of things that aren’t serving you anymore.
- Use Multi-Factor Authentication (MFA): For added security, require MFA for guests when logging in. It’s an extra barrier against those pesky unauthorized accesses.
- Educate Guests: Provide guidelines about security practices so that guests know how to handle sensitive information while they’re hanging out in your digital space.
These steps help keep everything running smoothly while protecting both your organization and your guest users.
In my experience working with guest accounts, I once helped set one up for a freelance designer we were working with for a short project—a creative endeavor that needed sharing files and feedback quickly without the hassle of setting up new user credentials. The whole process felt seamless! What could’ve been complicated was made simple by just focusing on permissions and clear communication about roles.
In summary, managing guest accounts efficiently isn’t just about sharing access; it’s about balancing collaboration with security. When done right, it can be beneficial for everyone involved!
Understanding Microsoft Guest Account Login: Legal Implications and Best Practices
Mastering Microsoft Guest Account Login: Features, Benefits, and Setup Guide
Microsoft’s guest account feature can be super useful for sharing access without compromising your main account’s security. You might find yourself needing a way to let someone access files, collaborate on projects, or use applications without giving out your password or full access. Pretty neat, huh? But there’s more to it; you’ve got to be aware of some legal implications and best practices when setting things up.
So, what’s the deal with these guest accounts? Basically, they’re designed for temporary use. You create an account specifically for guests, allowing them to log in without messing with your usual settings or personal data.
Legal Implications
When it comes to legal stuff, you really want to think about who can access what through these accounts. If a guest uses your device and accesses sensitive info—whether intentionally or not—it could lead to issues down the line. Say you’ve got confidential company documents on your machine; if a guest accidentally stumbles upon them, that could create a whole mess! So it’s wise to set strict permissions.
Best Practices
To keep everything running smoothly and securely with guest accounts, consider these key points:
Features & Benefits
Using Microsoft Guest Accounts comes with some cool features too:
– Easy setup: Seriously, it’s not rocket science! Just follow prompts in the settings.
– Custom permissions: Tailor what each guest can see and do.
– Collaboration made simple: Perfect for sharing files while still keeping your info safe.
Let’s say you’re working on a project with a freelancer. By using a guest account for them instead of giving full access to your main profile, you maintain better control over sensitive data. Like I said earlier; it’s all about restricting access properly!
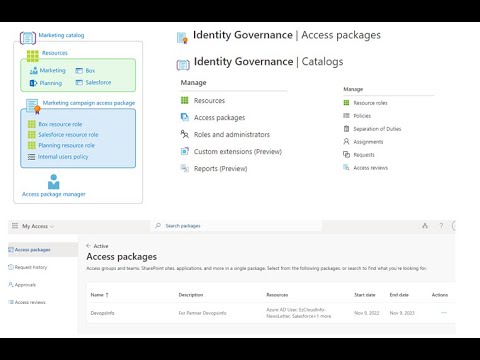
If you’re diving into **Azure’s Guest Account setup**, things get even cooler since it’s built with security as the priority. Azure lets you configure user roles and enforce policies right from their admin center.
Remember that when setting up any account—guest or otherwise—keeping cybersecurity in mind goes a long way! After all is said and done, ensuring that both you and your guests feel secure is super important.
So yeah, kind of a lot here but understanding how Microsoft Guest Accounts work helps keep your stuff safe while still allowing necessary collaboration!
Setting up a guest account in Azure kind of reminds me of that time I had to let a friend borrow my laptop. You know, the whole “I trust you, but I’m still a little paranoid” feeling? Yeah, that. So when it comes to giving someone access to your Azure resources—even if they’re just a guest—it feels like you’re walking a tightrope between security and convenience.
So, let’s break it down. First off, you’ve got to decide what resources your guest needs to access. Like, are you handing over your entire digital house or just letting them peek at the living room? Knowing what they need can really help tailor their access without compromising everything else.
Then comes the actual setup part. When you create that guest account in Azure Active Directory, it’s pretty straightforward. You invite them with their email address, and they get an invitation link. It’s like sending an invite for a dinner party—but instead of roasted chicken and awkward small talk, it’s about digital assets and permissions. But here’s where you’ve got to keep alert; it’s super important to assign the right permissions from the get-go. If you give them too much power accidentally? Well… let’s just say things could turn into a chaotic mess real quick.
And oh man, don’t overlook security! Azure has loads of features like multi-factor authentication (MFA). Seriously, think of MFA as your digital bouncer saying “not so fast!” That added layer of protection keeps things nice and secure.
After setting everything up, it’s always a good idea to revisit those permissions down the road—like checking in on how that friend is treating your laptop! You might find that they don’t need as much access as they initially did or maybe even need more depending on their role changing over time.
You see how all this works together? Setting up those guest accounts isn’t just about clicking some buttons; it involves contemplating who gets what access and ensuring everything remains safe while still being user-friendly. At the end of the day, it’s all about balancing trust with security—much like lending out your gear but making sure you’ve put everything away before handing over the key!