You know, working with DotNet can be a blast, right? But there’s a catch. Security is key.
I mean, who wants their app getting hacked? Seriously! It’s like leaving your front door wide open and expecting nothing to happen.
So, what can you do? Well, there are some best practices that can keep your project safe and sound.
Think of it as giving your code a solid little shield. Let’s chat about it—no jargon, just real talk on keeping everything secure while you’re developing. Sound good?
Comprehensive Guide to .NET Security Best Practices on GitHub
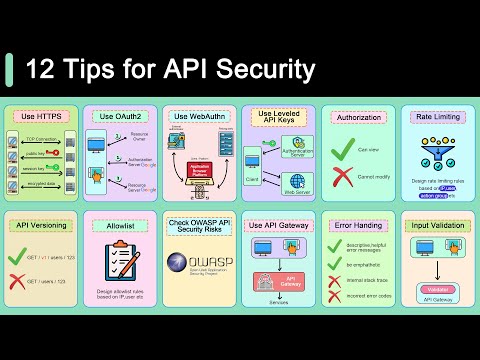
When it comes to securing your .NET applications, following best practices is key. Security isn’t just a checkbox; it’s an ongoing process that helps protect your data and users. Here’s a look at some solid .NET security best practices you can use, especially if you’re sharing your code on platforms like GitHub.
Input Validation
One of the biggest vulnerabilities in any application is bad input. You want to make sure that any input from users is validated thoroughly. This means checking it against expected formats and lengths before using it. For example, if you’re expecting an email address, ensure it follows the standard pattern.
Authentication and Authorization
These are two sides of the same coin but super crucial for security. Make sure that users are who they say they are with strong authentication methods. Use things like multi-factor authentication (MFA). Once authenticated, make sure you have proper authorization checks in place to control what users can do within the app.
Use Secure Connections
Always use HTTPS for your web applications. This encrypts data sent over the network, making it harder for attackers to eavesdrop on sensitive information like passwords or personal data.
Error Handling
Never expose sensitive information through error messages. Instead of showing technical details that could help an attacker, log errors internally and show user-friendly messages to front-end users.
Keep Libraries Updated
Third-party libraries can introduce vulnerabilities if they aren’t kept up-to-date. Regularly check for updates in your NuGet packages and apply them promptly when security patches are released.
Code Reviews
Encourage team code reviews where peers can check each other’s work for potential security flaws or weaknesses in logic. It’s amazing how another pair of eyes can catch something you might have missed!
Environment Configuration
Make sure that sensitive configurations (like database connection strings and API keys) aren’t hardcoded into your app but stored securely, like in environment variables or secure vaults.
Avoid Excessive Permissions
Run your applications with the least privilege necessary for them to function properly. So if something goes wrong, it limits what an attacker can do if they exploit a vulnerability within your app.
In summary, staying on top of these .NET security best practices will not only help safeguard your application but also build trust with your users. Sharing this knowledge on platforms like GitHub isn’t just about showcasing code; it’s about showing you care about security too!
Asp.Net Security Best Practices: Essential Strategies for Protecting Your Web Applications
Sure! Let’s break down some essential strategies for securing your ASP.NET applications. It’s super important to keep your web apps safe from this or that kind of threat, you know? So, here are some best practices you should consider.
Input Validation
Always validate user input. Seriously, it’s like the first line of defense. You don’t want folks sneaking in unwanted data. Implement whitelisting to only allow acceptable characters and patterns. For example, when a user enters an email address, make sure it’s in a valid format before you even think about processing it.
Authentication and Authorization
You need to ensure that users can only access what they’re allowed to. Use robust authentication mechanisms like ASP.NET Identity. Don’t just settle for simple password checks; think about two-factor authentication as well. You want to double-check who they say they are!
When it comes to authorization, always use roles or claims-based checks to restrict access. For example, if someone is trying to reach an admin page but they’re just a regular user? Nah, not happening.
Session Management
Secure your session management too. Do things like setting HttpOnly and Secure flags on cookies so they aren’t easily stolen through XSS attacks. Also, consider implementing session timeouts—it’s frustrating but worth it! Automatically logging out users after a period of inactivity helps prevent unauthorized access if someone leaves their computer unattended.
Error Handling
You wanna handle errors delicately. Don’t display raw error messages to users because that’s like handing potential attackers a cheat sheet! Instead, log those errors somewhere safe and show generic messages to users. Like “Something went wrong; try again later.” It keeps things under wraps.
Password Storage
If you’re storing passwords (which you definitely are), do it right! Use scrypt, Bcrypt, or other strong hashing algorithms with proper salting techniques. Just hashing isn’t enough; someone could easily crack weak hashes nowadays.
CORS Policy Configuration
Cross-Origin Resource Sharing (CORS) needs careful configuration. Allow resources only from trusted domains—don’t just open the floodgates for any origin! This helps prevent Cross-Site Request Forgery (CSRF) attacks that could mess things up badly.
Sensitive Data Transmission
Always transmit sensitive data over HTTPS. It encrypts the data in transit so that no one can snoop in on what’s going back and forth between your server and the client browser!
Patching and Updates
Keep everything updated! Your software libraries and frameworks should be patched regularly against known vulnerabilities—it’s like getting regular check-ups at the doctor’s office but for your codebase!
So there you have it: essential strategies for protecting your ASP.NET applications. Keeping security practices tight is pretty crucial—every little bit counts! Just imagine waking up one morning discovering you’ve been hacked because you didn’t take these steps seriously… not cool at all!
Essential C# Security Best Practices for Robust Application Development
When you’re writing applications in C#, keeping your software safe is super crucial. You don’t want your code to be the weak link that lets hackers sneak in. So, let’s dig into some vital security practices for C# development that can help you create robust applications.
1. Input Validation
Always validate user input! This means checking if the data coming into your system is what you expect. If a user inputs something like a username, make sure it only contains valid characters. Seriously, you don’t want malicious scripts slipping through because you didn’t filter inputs properly.
2. Use Strong Authentication
Password security is key! Instead of just using plain text passwords, consider hashing them using methods like SHA-256. This way, even if someone gets access to your database, they won’t see actual passwords—just hashed values which are way harder to crack.
3. Secure Data Transmission
When sending data over the internet, always use secure protocols like HTTPS instead of HTTP. This encrypts the data in transit and stops eavesdroppers from seeing what’s being sent back and forth between users and your server.
4. Exception Handling
Be careful with how you handle exceptions. If an error occurs and you’re not careful about what messages you show the user or log, you might inadvertently leak sensitive information about your application or its infrastructure.
5. Keep Libraries Updated
You know those libraries and frameworks that you use? They can have vulnerabilities too! Regularly check for updates to ensure you’re getting the latest security patches. Running outdated versions might leave open doors for attackers.
6. Principle of Least Privilege
Only give users and components the permissions they absolutely need to function—nothing more! If an application doesn’t need admin rights to work, then don’t give it admin rights.
7. Use Security Features
.NET has built-in features designed for security purposes—like UserSecrets for secret management during development or ASP.NET Identity for managing user authentication safely. Take advantage of these tools!
8. Regular Security Testing
Testing is not just for bugs! Make sure to regularly perform security testing and audits on your applications while also considering penetration testing where ethical hackers attempt to exploit vulnerabilities.
These practices may seem like a lot at first glance, but incorporating them into your development process will go a long way in creating secure C# applications. With all this in mind, think back on that time when everything crashed because of a simple oversight—it doesn’t have to happen again! By following these guidance points diligently, you’ll help keep your app safe from unwanted intrusions and potential disasters down the line.
DotNet security is like that invisible shield you wish you had when you’re walking through a dark alley. You know, it’s there, but if you don’t pay attention to it, you could be in for a surprise. I remember one time I was working on a project using .NET, and I thought everything was perfectly fine until I noticed some weird behavior with user data. Let me tell you, it was a stressful couple of hours digging through the code!
When it comes to security best practices in DotNet, it’s all about being proactive rather than reactive. You really need to keep an eye on things like input validation—this is where you make sure that whatever users are sending your way is not going to wreak havoc on your system. If someone tries to throw in malicious code through a form field, you want to catch that before it even gets processed.
Another biggie is using the right authentication and authorization methods. It’s kind of like having locks on your doors and knowing who has the key. You wouldn’t just give anyone access to your home, right? So apply similar logic here—make sure only the right folks have access to sensitive areas of your application.
Oh, and let’s not forget about keeping your libraries up-to-date! I once got into trouble because I neglected this. One outdated library led to a vulnerability that almost made my app an easy target for attackers. It’s like letting someone sneak into your house because you forgot to check if the windows were secure.
And serious consideration should be given to error handling too—you don’t want to spill all the beans about how your app works when something goes wrong! It’s kind of like keeping things under wraps during an awkward moment; sometimes silence is golden.
So yeah, understanding DotNet security best practices isn’t just some boring technical mumbo jumbo; it’s essential if you want your application—and its users—to stay safe from threats lurking around every corner. Each step might feel small at first, but they add up quickly into that robust fortress we all want our apps to be!