So, here’s the deal. You know how you lock your front door when you leave the house? Well, encryption is kind of like that for your data. It keeps your info safe from nosy folks trying to snoop around.
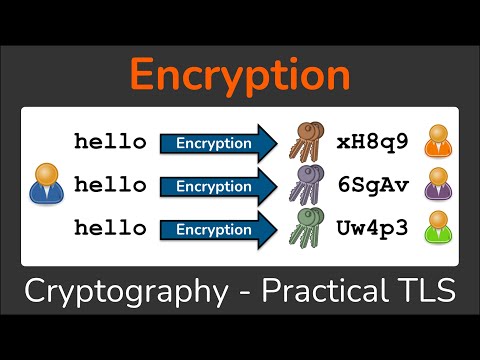
Imagine you’re sending a super-secret message to a buddy. You wouldn’t want just anyone reading it, right? That’s where encryption steps in. It jumbles everything up so only the people who know the magic code can read it.
In this chat about encryption methods, we’ll break it down in simple terms. No tech jargon here, just the juicy bits on how to keep your data under wraps. Let’s get into why encryption really matters and how it works!
RSA vs. AES: A Comprehensive Comparison of Encryption Techniques
Encryption is a big deal when it comes to keeping our data safe. If you’ve ever wondered about RSA and AES, you’re in the right place. Both are popular encryption methods but serve different purposes. So, let’s break it down.
RSA stands for Rivest-Shamir-Adleman, named after its creators. It’s what we call an **asymmetric encryption** method. This means it uses two keys: a **public key** and a **private key**. The public key encrypts the data, while the private key decrypts it. So if you want to send a secret message to a friend, you’d use their public key to encrypt it. Only they can unlock it with their private key.
On the other hand, we have AES, which stands for **Advanced Encryption Standard**. This one is all about **symmetric encryption**. Here, the same key is used for both encrypting and decrypting data. It’s like having one secret password that both people know to access a locked treasure chest.
Now, why does this matter? Well, let’s consider some important points:
- Speed: AES is generally faster than RSA. Since AES uses one key and simpler algorithms compared to RSA’s two-key system, it’s quicker for processing large amounts of data.
- Security Level: Both are considered secure but in different contexts. RSA relies on large prime numbers – breaking its encryption would take an insane amount of computing power. AES uses fixed block sizes and can be very secure if done right.
- Use Cases: RSA is typically used for securely exchanging keys or small bits of information like signing documents or establishing secure connections (think HTTPS). AES excels in encrypting entire files or large streams of data.
- Key Length: RSA requires much longer keys (2048 bits or more) to achieve similar security levels as shorter AES keys (128 bits being common). That’s why RSA can feel slow when handling bigger tasks.
So think about that moment when you’re backing up important files or chatting online with someone special—encryption plays a crucial role in keeping your info private.
In practice, many systems combine both methods: they use RSA to exchange an AES key securely and then switch over to AES for actual data encryption because it’s just faster for bigger stuff.
In short, understanding RSA vs AES gives you insight into how your data is protected every time you hit send or save something important on your devices! It’s all about using the right tool for the job at hand.
Understanding TLS and AES 256: Key Technologies for Secure Communication
So, when you’re browsing the web, sending emails, or making online purchases, you want to know your data is safe, right? That’s where encryption methods come into play. Two big players in this area are TLS (Transport Layer Security) and AES 256 (Advanced Encryption Standard with a 256-bit key). Let’s break these down.
TLS: What It Is
TLS is like a security blanket for your online communications. It encrypts the data being sent between your computer and the server. This means that even if someone tries to snoop on your connection, they can’t make sense of what you’re sending or receiving. It’s crucial for protecting personal information like passwords or credit card numbers.
You’ve probably noticed that when you visit a website and see “https” instead of “http,” it’s using TLS. The “s” stands for secure, which is pretty reassuring, isn’t it?
AES 256: The Heavy Hitter of Encryption
Now about AES 256—it’s a robust encryption standard used worldwide. Imagine this as the vault where you store all your precious documents. The «256» part refers to the size of the key used to encrypt your data; it’s really strong because it has a ton of possible combinations—like way more than there are stars in the sky!
AES 256 works by taking your data and scrambling it into an unreadable format. Only someone with the right key can decode it back to its original form. This makes it super effective against hackers who might want to steal sensitive information.
How They Work Together
So how do TLS and AES 256 work together? Well, think of it like this: when you connect to a secure site, TLS kicks in first to establish that secure connection using an encrypted channel. Within that channel, AES can be used to encrypt individual pieces of data sent over it.
Here’s what happens step-by-step:
- The connection is initiated: Your browser contacts the server.
- TLS handshake: They agree on how they’re going to communicate securely.
- AES encryption: Once everything’s set up, they use AES 256 to encrypt messages exchanged during the session.
This whole process means that whether you’re sending messages or entering credit card info on a checkout page, your data stays protected from prying eyes.
Why It Matters
In our digital world where everything feels so exposed sometimes, knowing about these technologies helps us understand how our information is being kept safe. Cyber threats are real; hackers are always looking for weak spots in our defenses. Understanding tools like TLS and AES 256 gives you peace of mind knowing there are strong measures in place protecting your info.
So next time you’re browsing securely or making an online transaction, remember: behind that comfortable layer of security lies some serious technology working hard so you don’t have to worry!
Understanding Basic Encryption Methods: Safeguarding Your Data in the Digital Age
When you’re navigating through the wild world of the internet, it’s super important to keep your information secure. I mean, think about it: you wouldn’t leave your front door wide open, right? Well, that’s kinda what happens when you don’t use encryption. So, let’s break this down a bit.
Encryption is like putting your data inside a locked box. Only those with the right key can open it and see what’s inside. There are a couple of basic methods out there that you’ll come across.
- Symmetric Encryption: This is where you use the same key for both locking (encrypting) and unlocking (decrypting) your data. It’s fast and efficient but has a downside—sharing that key can be risky. If someone intercepts it, they can access all your stuff.
- Asymmetric Encryption: Here’s where it gets interesting! You’ve got two keys: a public key (which anyone can see) and a private key (which you keep secret). You lock things up with the public key, and only the private key can unlock it. This method is safer for sharing information since you don’t have to send around sensitive keys.
- Hashing: Sometimes, you don’t actually need to recover the original data; you just want to confirm it hasn’t changed. Hashing takes an input and runs it through a cryptographic function to create a fixed-size string of characters. Think of this as creating an ID badge for your data—it proves its authenticity without needing the actual data back.
So why does any of this matter? Well, consider this: imagine you’re sending sensitive emails or storing files in cloud services; if those aren’t encrypted, they’re vulnerable to prying eyes. A few months ago, my friend had their email hacked because they didn’t use encryption for sensitive info—it was like leaving their diary lying around for anyone to read!
Now let’s chat about real-world examples. Websites using HTTPS are leveraging encryption; that “S” stands for secure! It ensures that any data sent between you and the site is encrypted, keeping snoopers at bay while you’re shopping online or logging into accounts.
Encryption can seem like one of those techy buzzwords that you hear tossed around but never really dive into. I remember when I first heard about it—some friend was talking about how their bank used it to protect their information. I thought, “That sounds smart, but why should I care?” Fast forward a few years, and here I am, deep in the rabbit hole of online security.
So, what’s the deal with encryption anyway? Think of it like a secret code for your digital information. When you send an email or upload files, encryption scrambles your data into a format that looks like gibberish to anyone who might intercept it. Only those with the right decryption key can unscramble it and read it again. It’s all about keeping your stuff safe from hackers or snoopers.
There are a couple of main types of encryption you might hear about: symmetric and asymmetric. With symmetric encryption, the same key is used to lock (or encrypt) and unlock (or decrypt) the data. It’s like having one key for your house; you use that same key whether you’re coming or going. Asymmetric encryption, on the other hand, uses two keys—one public and one private. The public key locks things up so anyone can use it to encrypt messages sent to you, but only you can unlock them with your private key. Kind of cool how that works!
But honestly, what strikes me most is how crucial this stuff has become as we do more online these days—even just browsing Facebook or shopping on Amazon means sharing personal info that could fall into the wrong hands if not protected properly.
And then there’s that real-world aspect: imagine waking up one day only to find out your bank account had been drained because someone got hold of your sensitive info! Yikes! It really drives home why understanding how encryption works is not just for tech-savvy folks anymore; it’s for everyone who wants to feel secure in our digital world.
In short, being informed about encryption isn’t just some nerdy pastime; it’s kind of essential today. Like learning to lock your doors at night—it just makes sense! So yeah, diving into these methods isn’t just smart—it’s empowering too!