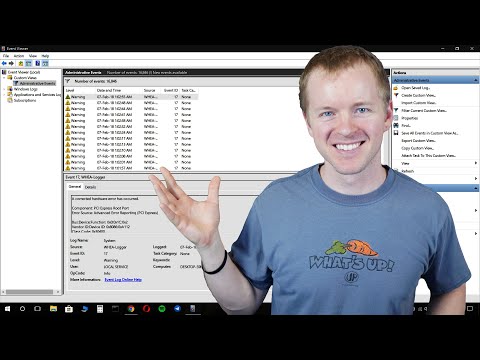
So, you know that little tool in Windows called the Event Viewer? It’s like this hidden treasure chest of info about your computer’s goings-on. Seriously!
When something goes wrong, it can feel like searching for a needle in a haystack. You’re there, trying to figure out what’s up with your PC, and all you get is confusion!
That’s where Event Viewer steps in. It logs everything your computer does—errors, warnings, even little tidbits about its daily life.
If you want to troubleshoot like a pro or just understand what’s happening behind the scenes, getting cozy with these logs is key. So let’s break it down together!
Understanding the Three Primary Event Logs: A Comprehensive Guide
Understanding event logs can seem a bit overwhelming at first, but once you get the hang of it, they’re super helpful for troubleshooting issues on your PC. The Event Viewer is like a diary for your computer, keeping track of all sorts of events that happen behind the scenes. There are three primary event logs you should know about: the Application log, the System log, and the Security log. Let’s break them down!
The Application log records events related to software applications. This includes errors from programs you run, warnings about potential issues, and informational messages that can be useful to developers or support specialists when tracking down bugs. For example, if you’re getting crashes in a specific app, checking out this log can provide clues to what’s going wrong.
Then there’s the System log. This one keeps tabs on Windows system events. It records information about hardware failures, driver issues, and things like service failures or startup problems. So if your computer is acting up during boot-up or disconnecting from devices unexpectedly, peeking into this log might show if there’s something funky going on with your drivers or system services.
Now onto the Security log. This one is all about security events like login attempts and access rights. If you’re worried about unauthorized access to your machine or just want to keep an eye on who logged in when—this is where you’ll look. It’ll tell you all about successful and failed login attempts along with other security-related activities.
To sum it up:
- Application Log: Focuses on application-specific events.
- System Log: Captures Windows system-related events.
- Security Log: Deals with security-related activities.
Diving into these logs can feel daunting but don’t stress! With time, you’ll realize it’s just a matter of getting familiar with what’s where. And believe me, knowing how to navigate these logs can save you so much headache in troubleshooting—whether it’s fixing crashes or locking down your security settings!
Understanding the Key Differences Between 4732 and 4728: A Comprehensive Guide for Legal Professionals
Comparative Analysis of 4732 and 4728: Insights into Technological Distinctions and Applications
Understanding Event Viewer Logs: What’s Up with 4732 and 4728?
So, when you dive into the Event Viewer Logs in Windows, you might come across events like 4732 and 4728. Both of these fall under the category of security-related logs, but they’re there for different reasons. Knowing what each one represents can really help you when troubleshooting or tracking down what’s going on within your domain.
Event 4732 is all about adding a member to a group. Specifically, it tells you when a user gets added to a security-enabled local group. This log is super handy if you’re managing permissions and trying to keep track of who can do what within your system or network.
On the flip side, we have Event 4728. This event logs when a member is added to a global group in Active Directory. Basically, it covers a broader scope because it involves groups that could potentially affect more users and systems across the whole directory.
Here’s how they differ fundamentally:
- Scope:
- 4732: Affects only local groups.
- 4728: Deals with global groups within Active Directory.
- Context:
- User-Related Actions: Both events track user actions, but in different capacities.
- AUDIT_LOGGING: If you’re auditing changes closely, each event gives distinct insights.
- Use Cases:
- If you see an unexpected entry in 4732, it may indicate unauthorized access or privilege creep.
- A suspicious addition in 4728 can mean someone is trying to escalate privileges on a wider scale.
Let me tell you—understanding these differences could save you from some pretty nasty security headaches. Imagine this: You check your Event Viewer log and find Event 4732 showing some strange activity late at night. Maybe someone added themselves to an admin group without permission! That sparks concerns about security in your environment.
Conversely, if Event 4728 logs show accounts being added to crucial global groups unexpectedly, that’s like finding out someone has keys to the entire building without telling anyone. It raises red flags!
In summary: while both events help paint the picture of what’s happening with user permissions and group memberships in your system, each serves its own purpose based on whether you are looking at local versus global contexts. It’s all about understanding that small difference so you can react appropriately!
Keep these distinctions in mind as you’re sifting through those logs next time—you’ll definitely feel more equipped to tackle any issues that may come up!
Top 10 Critical Windows Event IDs: Essential Insights for Monitoring and Security
When you’re digging into Windows Event Viewer, you’ll find it’s like a treasure trove of information about what’s happening behind the scenes on your PC. Event IDs, in particular, can give you vital info for monitoring system health and security. Let’s chat about some critical ones that you ought to know.
Event ID 4624 – This one’s about successful logons. Whenever someone logs onto the system, this event gets triggered. It’s crucial for tracking who accessed your computer and when. If you’re ever suspicious about unauthorized access, check here first.
Event ID 4625 – On the flip side, this ID shows failed logon attempts. It tells you when someone tried to log in unsuccessfully. If you see a bunch of these from the same IP or user account, it could be a sign that someone’s trying to break in.
Event ID 4648 – This event is recorded when a logon attempt happens using explicit credentials. Basically, if someone tries to use another user’s login details, it gets flagged here. You might want to pay attention to these if you’ve got users sharing accounts or passwords—yikes!
Event ID 4688 – This one tracks new process creation, which is super useful for spotting unauthorized or suspicious software running on your machine. Let’s say you didn’t install anything new but are seeing unexpected processes; checking this event can give you some clues.
Event ID 4720 – Here we have account creations; every time a new user account gets created on your system, it’s logged with this ID. It helps ensure that no rogue accounts are made without your knowledge.
Event ID 4726 – Just as important as creating accounts is deleting them! This event gets logged whenever an account is removed—which means if there are any disappearing users that shouldn’t be gone, you’ll find out through this event.
Event ID 5156 – This one deals with network connections being allowed through Windows Firewall. If something suddenly pops up here that looks unusual—like connections from weird IPs—you should probably investigate further.
Event ID 5140 – It monitors file share access attempts; every time someone tries to use shared files over the network—successful or not—this gets logged. If there’s unusual file access happening at odd hours—it’s worth looking into.
Event ID 8003 – This logs when network computers are discovering each other over the protocol used by Windows (like WINS). If there’s chatter happening more than usual across devices on your network, this could be a helpful clue.
Finally, Event ID 1102, which signals that the audit log has been cleared! Clearing logs can mask bad behavior on a system and should always raise red flags; keep an eye out for this one!
So basically, keeping tabs on these critical event IDs can really help secure your machine and handle issues before they get out of hand. You follow me? Checking these logs shouldn’t feel like a chore—it can save you from headaches down the line!
You know, I remember the first time I heard about Event Viewer. I was struggling with my laptop crashing multiple times a week, and someone casually said, “You should check the Event Viewer logs.” I had no clue what that was, but I nodded along like I understood—classic me!
So, what’s the deal with Event Viewer? Basically, it’s like a digital diary for your computer. It keeps track of everything that’s happening under the hood. You’ve got system events, application logs, and security logs all jumbled together like a giant tech stew. Each entry is a little nugget of information that can help you figure out what’s gone wrong when your machine suddenly decides to take a break.
When you open Event Viewer, you might feel overwhelmed at first. It can be a bit dense with all those lines and numbers staring back at you. But once you get the hang of it, it’s like finding treasure! Imagine you’re on a scavenger hunt; each log entry is a clue leading to the answer you’re looking for. Let’s say your printer’s acting up again—guess where you might find out why? Yup! You can dig into those logs to see if there was an error message regarding communication issues!
A while back, my friend called me in tears because her computer wouldn’t start after an update. We were both panicking until I remembered Event Viewer could help us out. After some digging through the logs, we found an error about a driver conflict related to her graphics card. With some simple adjustments and updates later on—boom! Her laptop was working again.
So really, getting comfortable with Event Viewer isn’t just about knowing what went wrong; it’s also about empowering yourself to troubleshoot effectively next time something goes haywire. You might even feel like a tech wizard once you unravel those confusing codes! Just remember that every entry is there for a reason—it tells your computer’s story one event at a time.
And if nothing else, digging through those logs gives you something to do while waiting for your device to restart… which happens way too often anyway!