Hey! So, let’s chat about something that’s super relevant these days: cyber threats. They’re everywhere, right?
I mean, just the other day, a friend of mine panicked because his email got hacked. Yikes! What a nightmare. It made me think about how crucial it is to keep our networks safe.
Enter Fortigate! This tool packs some serious punch when it comes to threat management features. It’s like having a security guard for your digital space.
So, if you’re curious about how it all works—what those fancy features really mean for you—you’re in the right place! Let’s break it down together!
Understanding the 4 Essential Steps of Threat Management in Legal Contexts
Mastering the 4 Key Steps of Threat Management in Technology Solutions
Threat management in the legal context is super important. With all the tech we use these days, it’s crucial to know how to protect sensitive information and stay compliant with laws. So, let’s break down the four essential steps of threat management, especially when thinking about things like Fortigate’s features.
- Identification
The first step is all about spotting potential threats. This means figuring out what risks your organization might face. For example, are you dealing with sensitive client data? You need to know if there are vulnerabilities in your system that could be exploited by a hacker or even an insider threat.
Think of it like this: when I first set up my home Wi-Fi, I didn’t even think about securing it properly. But after realizing someone could hop onto my network and snoop around, I had to take a closer look at what I was protecting.
- Assessment
Once you’ve identified potential threats, you need to take stock of their impact. Not all risks are created equal! Some may result in minor inconveniences while others could lead to major legal troubles or loss of trust. Evaluating these threats helps prioritize what needs immediate attention.
You might ask yourself questions like: What would happen if our client data was leaked? How would it affect our reputation? This type of assessment is critical for setting up a solid defense.
- Mitigation
Now that you know what you’re dealing with and how serious each threat is, it’s time to put some measures in place to mitigate those risks. This might involve implementing security protocols or using tools like Fortigate that can help block incoming attacks or filter out harmful traffic.
Having firewalls and intrusion detection systems can seriously reduce risks. It’s kind of like putting up fences around your yard—nice but not foolproof! You really want layers of security as backup because threats evolve over time.
- Monitoring & Response
The final step involves ongoing monitoring and being ready to respond if something goes wrong. It’s not enough just to set things up once and forget about them! Regularly checking logs and alerts helps catch any suspicious activities early on.
If an incident does occur—like a data breach—it’s crucial to have an action plan ready so that you can respond quickly. This includes notifying affected parties or legal authorities as needed based on relevant laws (like GDPR or HIPAA).
So yeah, keeping an eye on stuff is just as vital as the initial setup! You don’t want any surprises popping up later on down the road.
In short, mastering these four steps—identification, assessment, mitigation, and monitoring & response—helps ensure that your organization stays secure while navigating the complex landscape of technology solutions in legal contexts. And using features from tools like Fortigate can make this process smoother by providing better visibility and control over your network security!
Understanding the 4 Types of Threat Detection: A Comprehensive Guide for Legal and Technology Professionals
In today’s digital world, understanding threat detection is super important for anyone involved in tech or law. Basically, threat detection helps keep systems safe from various attacks and vulnerabilities. Fortigate offers some handy features to assist in this area. Let’s break down the four main types of threat detection you should know about.
1. Signature-Based Detection
This method relies on known patterns of malicious code or behaviors. Think of it like having a list of wanted criminals: if something matches a pattern, it gets flagged. For example, if a piece of malware has been previously identified and its “signature” is stored in the system, the detection tool can catch it right away.
2. Anomaly-Based Detection
Now, this one’s kind of interesting because it looks for deviations from normal behavior. It sets a baseline for what «normal» traffic looks like and then says, “Hey! What’s that strange activity?” If your network usually sees low data transfers at night and suddenly there’s a spike, anomaly-based detection raises a flag. It helps catch new threats that might not have an established signature yet.
3. Stateful Protocol Analysis
With this method, systems examine the state and context of network traffic to determine if it’s legitimate or malicious. Basically, it checks to see if packets within a session follow the rules set by the protocol being used. For instance, if you’re using HTTP but suddenly see some HTTPS packets that don’t belong in that session—red flag! This approach builds on both stateful inspection and deep packet inspection.
4. Heuristic-Based Detection
This one uses algorithms to identify potential threats based on their behavior rather than their appearance or origin—like having a good gut feeling about something fishy! Sometimes systems make educated guesses based on similarities with known malware behaviors. So even if there’s no exact match—for example—a new variant of malware might act similarly enough to get flagged.
Each type has its pros and cons, of course! Signature-based detection is quick but can miss new threats; anomaly-based works well for spotting zero-day exploits but might flag false positives quite often due to normal fluctuations in systems.
Fortigate incorporates these methods into its threat management features so you can adapt your defenses based on your specific needs—keeping you one step ahead of cybercriminals.
So there you have it! Understanding these four types lets legal and technology pros equip themselves with knowledge that directly impacts cybersecurity strategy and decision-making in their fields.
Understanding the Key Differences Between UTM and SIEM: A Comprehensive Guide
When you’re looking at cybersecurity, you often bump into terms like UTM and SIEM. Both are crucial for protecting your systems, but they’ve got different roles. Let’s break it down so it’s super clear.
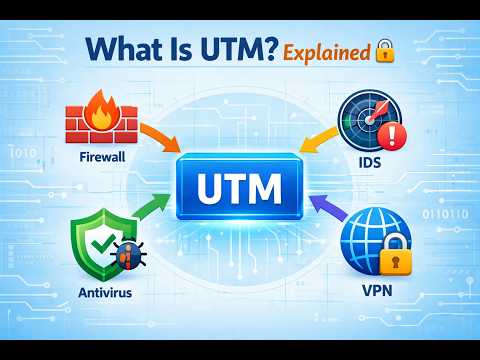
UTM (Unified Threat Management) is like a one-stop shop for security. It bundles multiple security features into a single device or software solution. Imagine it as a Swiss Army knife for your network’s protection. A typical UTM might include:
You get the idea! The strength of UTM is that it simplifies management since everything is centralized. So, if you’ve got a Fortigate firewall with UTM features, it basically helps to keep threats at bay through various means in one place.
Now, on the other hand, SIEM (Security Information and Event Management) focuses on monitoring and analyzing security events from multiple sources within your IT environment. Think of it as having a vigilant watchtower that looks out for anything suspicious happening in your network. SIEM collects logs and event data from different devices like servers, firewalls, and endpoints to do its magic.
Here’s what SIEM typically brings to the table:
With SIEM, you’re able to spot patterns over time or react quickly to potential threats because all that data is aggregated in one spot.
So why does this matter? Well, while UTM actively prevents intrusions by stopping them before they can cause damage, SIEM’s role kicks in once something has been detected or when you need to analyze past incidents.
Imagine you’ve set up Fortigate’s UTM features—it’s blocking harmful traffic like a pro—but then a user clicks on a phishing link when they’re not supposed to. This might go unnoticed until your SIEM tool flags an unusual spike in logins or detects an unauthorized access attempt.
In simple terms: UTM is about prevention, while SIEM is about detection and response. Both play pivotal roles in an organization’s cybersecurity strategy.
So yeah, if you’re diving into threat management using Fortigate’s features, understanding the difference between these two can really sharpen your approach! You’re not just throwing money at tools; you’re actually building an effective defense strategy by combining both prevention with real-time analysis!
So, Fortigate, huh? It’s one of those things that can sound super technical, but when you break it down, it really isn’t all that bad. Their threat management features are a big deal, especially if you’re into keeping your network safe. I remember once when I got my hands on a Fortigate device for the first time. It felt like cracking open a treasure chest of security tools.
Basically, what Fortigate does is help you manage and mitigate risks to your network. It’s like having a watchdog that barks at anything suspicious trying to sneak into your digital backyard. You’ve got firewalls doing their thing, protecting against unwanted access—not exactly the most exciting stuff but oh-so-important.
Then there’s intrusion prevention systems (IPS). It’s kind of like having a super-smart guard who not only sees someone trying to break in but can also identify if they’re carrying something dangerous or not. So if there’s suspicious activity, the system reacts quickly and shuts it down before it can do any harm.
Oh! And let’s not forget about antivirus protection—an essential in today’s world where malware seems to be lurking around every corner. Fortigate integrates this feature directly into its system so that you don’t have to juggle multiple security solutions. Seriously, dealing with different programs can be a pain in the neck!
Another cool thing is how Fortigate uses artificial intelligence for threat detection. Imagine having a buddy who’s always learning from past experiences—like when they warn you not to walk down that sketchy alley again because they know what happened last time! That’s what AI does here; it analyzes patterns and identifies potential threats more efficiently.
You know what’s wild? It’s not just about blocking threats; it’s also about visibility and understanding what’s happening in your network at any given moment. Real-time monitoring lets you see attacks as they happen—talk about being on top of things!
All in all, exploring Fortigate’s features gave me a lot more confidence about how we handle security issues today. So yeah, if you’re thinking about upping your security game or just curious about how these systems work, checking out threat management features will definitely broaden your perspective on what’s possible!