So, you’re diving into cloud stuff, huh? Pretty cool! You might have heard about VPC flow logs. They sound kinda technical, right?
But here’s the thing: they’re super important for security in cloud environments. Imagine having a magic window that shows you what’s happening in your virtual private cloud. Sounds neat, doesn’t it?
These logs can give you some serious insights, like traffic patterns or any weird requests that pop up. It’s like having a security camera at your digital front door!
But, and this is a big but, if mishandled or misunderstood, they can also lead to some major headaches. So buckle up as we dig into what these flow logs really mean for your cloud security!
Understanding Security Implications of VPC Flow Logs in Cloud Environments: A Comprehensive Example
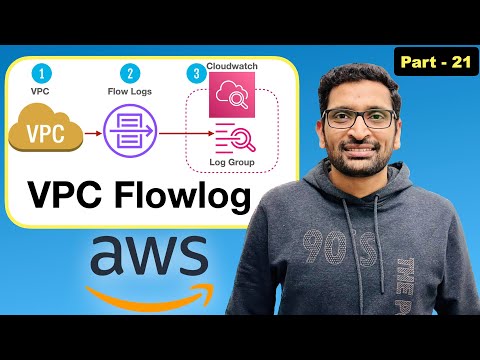
VPC Flow Logs are a vital tool when it comes to understanding the security implications of your cloud environment. They help you monitor the traffic coming in and out of your Virtual Private Cloud (VPC). So, you might be wondering why this matters. Well, it’s all about visibility and control. Let’s break it down.
First off, VPC Flow Logs capture information about the IP traffic going to and from network interfaces. This includes the source and destination IP addresses, ports, and protocols used. With this data at your fingertips, you’re able to see what’s happening in your VPC at any given moment.
But why is that important for security? Analyzing these logs can help identify unusual patterns or potential attacks on your cloud infrastructure. For example:
- If you notice a spike in traffic from an unknown IP address, that could signal an attempted breach.
- If certain ports are being targeted frequently, it’s a good idea to investigate further.
- You can also track denied connections that may suggest misconfigured security groups or network ACLs.
Understanding who accesses your resources is key. If you’re running web applications or sensitive services, knowing where your traffic comes from helps mitigate risks. Imagine finding out that a service exposed publicly is receiving requests from a suspicious location. That’s a red flag!
Next up is compliance. Many industries have strict regulations regarding data protection. Flow logs provide an audit trail showing who accessed what and when. This can be super handy during audits or if there’s ever a need for forensic investigation after a security incident.
Don’t forget about performance monitoring! Security isn’t just about preventing bad guys; it’s also about ensuring everything runs smoothly. Flow logs can reveal bottlenecks caused by unexpected traffic patterns which could impact performance—even if they’re not malicious!
A practical example: Say you have an application hosted in your VPC that’s supposed to handle user data securely. You set up flow logs to check activity related to this app. You notice unauthorized access attempts on nights and weekends when no one is around—like how creepy would that be? This insight allows you to take immediate action: perhaps tighten security groups or implement more stringent access controls.
Lastly, let’s talk cost management. While flow logs themselves don’t directly cut costs, analyzing them effectively can inform decisions around resource allocation—ensuring you’re only using what you need without falling victim to overprovisioning resources due to undetected usage spikes.
The bottom line? VPC Flow Logs are more than just passive records of network activity; they’re active tools for enhancing security postures in cloud environments! If you’re not already leveraging them for these purposes, now’s the time to start thinking about how they can fit into your security strategy.
Exploring Security Implications of VPC Flow Logs in Cloud Environments: A Comprehensive Guide
VPC flow logs are like the security cameras of your virtual private cloud. They keep track of all the traffic going in and out of your cloud resources, which is super helpful when it comes to maintaining security. So let’s dig a little deeper into the implications these flow logs have on security.
First off, what are VPC flow logs? Well, they record information about the IP traffic traveling to and from network interfaces in your VPC. This includes details like source and destination IP addresses, ports, protocols, and whether the traffic was allowed or denied by your security groups or access control lists. You follow me?
Now, why are these logs important for security? Think of them as your first line of defense. Analyzing flow logs helps you spot unusual patterns that might indicate a potential breach or attack. For instance:
So, you can see how monitoring these logs is vital for keeping things secure!
However, just having the flow logs isn’t enough; you need to analyze them regularly. It’s not unlike checking in on those security camera feeds after hearing strange noises outside at night—you want to know what’s happening! That way you can act quickly if something fishy pops up.
Next up is storage and retention policies for these log files. This is crucial. You don’t want important info getting lost because old logs were deleted prematurely. Make sure you retain them long enough to investigate any incidents that may arise later on. Different regulations also dictate how long certain types of data need to be kept—so check those!
Finally, let’s touch briefly on compliance issues because they’re pretty big in cloud environments too. Depending on where you’re located or what industry you’re in, there might be laws about logging and monitoring network traffic. Ensuring that your VPC flow logging meets these legal requirements helps protect not only your data but also keeps you outta hot water with regulators.
Alright, let’s chat about VPC Flow Logs. If you’re working in a cloud environment, you’ve probably heard of these logs before. They’re like cameras keeping an eye on your Virtual Private Cloud (VPC) traffic, recording all the data flowing in and out. It’s pretty neat because you can see what’s going on, but there are some security implications that you should think about.
So, first off, let’s be real. With all that data pouring in, it can feel a little overwhelming. Imagine trying to find a specific moment in a long video – yeah, that’s how it is going through flow logs sometimes. But here’s the thing: while you’re sifting through that information, you’re also spotting potential security threats.
I remember when I first started using VPC Flow Logs for my projects. I was super excited to see the traffic patterns and ensure everything was running smoothly. But then I realized how much sensitive information could be at risk if someone unauthorized got access to those logs. You know? That moment hit me hard—like when your favorite show ends on a cliffhanger and leaves you thinking hard about what could happen next.
When these logs are stored without proper security measures, they can become targets for malicious actors looking to exploit vulnerabilities or gain unauthorized access. So keeping those logs secured is crucial! You have to think about access control strictly; not everyone should be able to view those logs. It’s like inviting folks over for dinner—you don’t want just anyone wandering into your kitchen, right?
Another thing you might want to consider is retention policy. Holding onto flow logs indefinitely sounds tempting since there might be useful info buried in them somewhere, but it also means more risk exposure over time. When you archive too much data without reviewing it regularly, it kind of becomes like hoarding junk—you might find something valuable occasionally, but mostly it’s just clutter.
And what about compliance? Depending on where you operate or who your customers are, certain regulations may require specific handling of log data. Not following these rules can lead to fines or other consequences that no one wants on their plate.
VPC Flow Logs can be powerful tools—really useful for monitoring and troubleshooting—but let’s not forget their security implications! Just like any part of your cloud setup needs careful attention and consideration so does the way we manage our flow logs. A little vigilance goes a long way in protecting not only your environment but also the privacy and security of your users’ data!